We have recently updated our company website and one of the benefits of the change is that we are now able to manage the Securlinx blog in our own hosting environment.
New posts will appear at Securlinx.com/blog.
Thursday, March 8, 2018
Tuesday, March 15, 2016
Amazon files mobile face recognition patent for payments
Amazon will soon accept mobile payments using selfies instead of passwords (Silicon Republic)
Amazon has filed a patent application for technology that will allow users to authenticate a payment using a photo or video in a seamless way that doesn’t necessarily require passwords.
“The user is identified using image information which is processed utilising facial recognition. The device verifies that the image information corresponds to a living human using one or more human-verification processes,” the patent reads.
Monday, March 7, 2016
"Holy Bat-phone, Batman!"
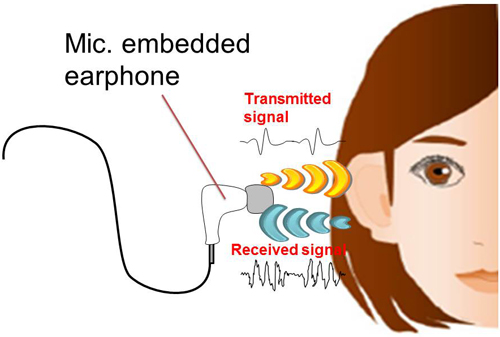
NEC develops biometrics technology that uses sound to distinguish individually unique ear cavity shape (NEC)
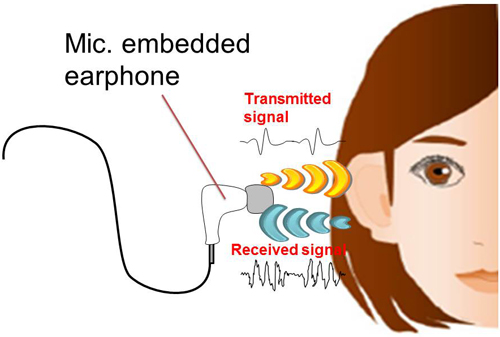
The new technology instantaneously measures (within approximately one second) acoustic characteristics determined by the shape of the ear, which is unique for each person, using an earphone with a built-in microphone to collect earphone-generated sounds as they resonate within ear cavities. This unique method for extracting features is useful for distinguishing individuals based on acoustic characteristics and enables rapid and highly accurate recognition (greater than 99% accuracy).
Friday, March 4, 2016
Illinois: Google faces face-rec lawsuit
Google Gets Sued Over Face Recognition, Joining Facebook And Shutterfly In Battle Over Biometric Privacy In Illinois (IBTimes)
In the latest scuffle over biometric data collection in Illinois, Google Inc. this week was hit with a lawsuit over its face-recognition technology, making Google the latest tech giant to be accused of violating an unusual state privacy law that restricts the collection and storage of so-called faceprints. Illinois and Texas are the only two states that regulate how private companies may use biometric data, and Illinois is the only state that authorizes statutory damages for violations.
Monday, February 29, 2016
Forecast: Global Biometrics Market in Hospitality Sector 2016-2020
Market outlook of the biometrics market in the hospitality sector (Research and Markets)
The market research analyst predicts the global biometrics market in the hospitality sector to grow at a CAGR of around 27% during the forecast period. With the increase in cases of time theft, data theft, and other criminal activities in the hospitality sector, the demand for security technologies including a highly reliable and accessible personal authentication and identification systems has increased. Biometrics has emerged as a suitable security and monitoring solution to meet this need as it is based on the behavioral and physiological characteristics of an individual, which is difficult to replicate. Biometrics in the hospitality sector is seen as the most accurate and reliable system because it eliminates manual inputs, identity card exchange, and time theft.
Biometrics for better government finances
Nigeria saves $11 million after removing 20,000 ‘ghost workers’ (Hindustan Times)
Nigeria’s government has removed more than 20,000 non-existent workers from its payroll following an audit, leading to savings of 2.29 billion naira ($11.53 million) from its monthly wage bill, the Finance Ministry said on Sunday.
...
The audit used biometric data and a bank verification number (BVN) to identify holders of bank accounts into which salaries were being paid.
The proof is in the fingerprint: how biometrics are proving security doubters wrong (memeburn)
Biometrics is not the uncharted Wild West or the strange cousin who lives next door, it is one of the fastest growing markets in the world because it works. It is also predicted to be worth around US$23.3 billion by 2019 with a CAGR of 20.8%. This is one market which is on a steady trajectory thanks to its potential and its ability to reduce fraud and data theft by significant amounts. The proof as they say, is not so much in the pudding as it is in the fingerprint…
Thursday, December 3, 2015
China: Arrests in US OPM case
Chinese government has arrested hackers it says breached OPM database (Washington Post)
Beijing has repeatedly insisted that the government played no role in the intrusions, which compromised sensitive personal, financial and biometric data of the employees, and data on their families.
Costs continue to mount from Target 2013 breach
Target settles for $39 million over data breach (CNN)
The settlement is the latest in a series of payouts Target has made.
In August, Target settled with Visa for $67 million over the data hack. And in March, Target settled a federal class action lawsuit brought by customers for $10 million.
Tuesday, November 24, 2015
Healthcare: Getting serious about multifactor authentication
The Time Has Come for Two-Factor Authentication in Health Care (iHealthBeat)
William Braithwaite -- a health information privacy and security consultant and chair of the Healthcare Information and Management Systems Society's identity management task force -- noted that, no matter how long or complex passwords are, they're still vulnerable to theft. "The real problem is that passwords are being stolen, not that they're being broken," he said.
Subscribe to:
Posts (Atom)
